Webinar Recap: CMMC False Starts and the Readiness Gaps Organizations Keep Missing
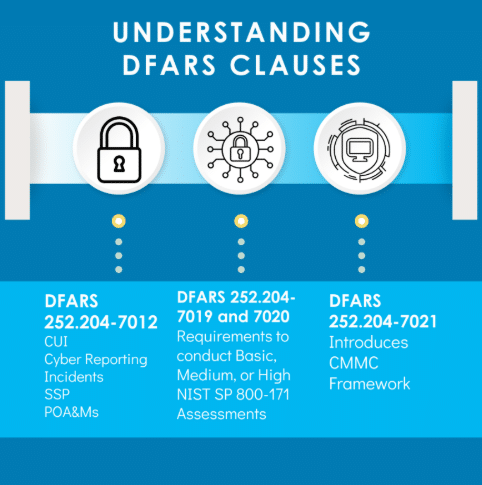
CMMC conversations across the Defense Industrial Base have entered a new phase. Certification requirements are now formally established, and organizations are currently grappling with timing,